I’ve spent over a decade advising businesses on IT strategy, and there is one conversation I have constantly. We spend so much time building robust enterprise architectures and massive firewalls, but then a senior manager sits down at a coffee shop, connects to “Free Public Wi-Fi,” and accidentally hands over the keys to the kingdom.
This happens through something called a Man-in-the-Middle (MITM) attack. It sounds like a plot from a spy movie, but it is one of the most common ways people get hacked today.
Let’s break down exactly what this is, how the bad guys pull it off, and—most importantly—how you can stop them, without the heavy technical jargon.
What is a Man-in-the-Middle Attack?
Think of it like the old postal service. You write a private letter to your bank and hand it to the postman. But instead of delivering it straight to the bank, the postman opens it, reads your account details, seals it back up, and delivers it. The bank thinks the letter came safely from you, and you think the bank received it securely. You are both wrong.
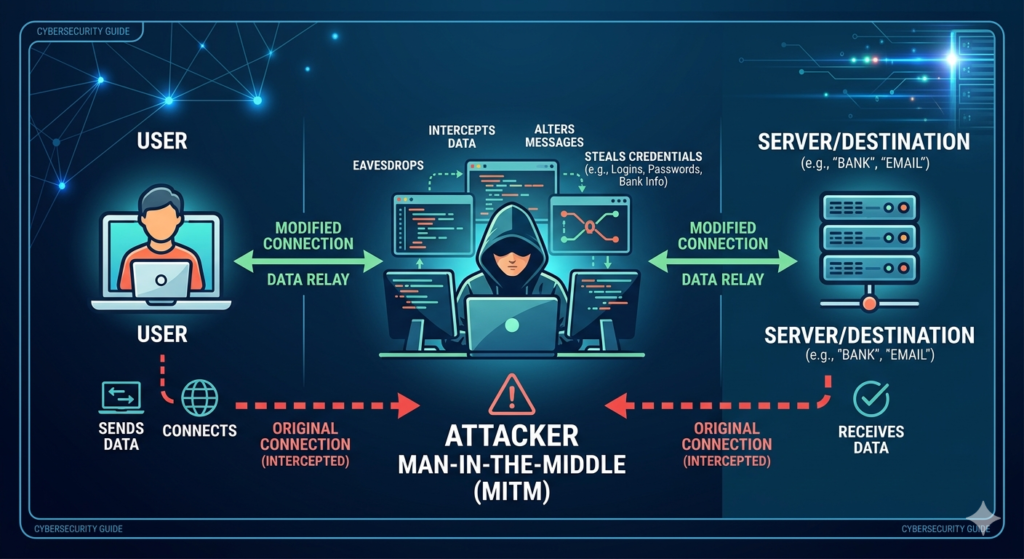
In the digital world, the “postman” is a hacker who has secretly positioned themselves between your device (like your phone or laptop) and the website or service you are trying to reach.
The bottom line: In a MITM attack, the hacker isn’t breaking into your computer or the bank’s servers. They are simply intercepting the traffic flowing between the two.
How the Trap is Set
These attacks don’t happen by magic. They require a bit of setup, usually targeting people who are traveling or working remotely. Here is the standard playbook:
1.Phase 1: Setting the Bait: The Rogue Hotspot.
The easiest way to intercept traffic is to control the network. A hacker sits in a busy public place and sets up a Wi-Fi hotspot on their laptop. They name it something believable, like “Airport_Guest_Network” or “Starbucks-Free-WiFi.”
2.Phase 2: The Interception: Listening In.
You walk in, see the free Wi-Fi, and connect. Now, every website you visit, every password you type, and every email you send passes through the hacker’s machine before it goes out to the actual internet.
3.Phase 3: The Exploit: Stripping the Security.
Even if you visit a secure site (one with a padlock icon), hackers use tools to quietly downgrade your connection. They strip away the encryption, allowing them to read your passwords and session tokens in plain text.
Real-World Examples
To picture how this looks in the wild, here are two common scenarios:
1. The “Evil Twin” Network
You are staying at a hotel and want to check some work emails. You connect to “Hotel_Lobby_WiFi.” What you don’t know is that the real network is “Hotel_Lobby_Guest.” The one you clicked belongs to a hacker sitting two sofas away. They watch your traffic, steal your Microsoft 365 login, and later use it to access corporate data.
2. The Fake Website (DNS Spoofing)
You are connected to a public network and type www.yourbank.com. The hacker’s software intercepts that request and redirects you to a site they built that looks exactly like your bank’s login page. You type in your password, hit enter, and it throws an “error.” You shrug it off, but the hacker just saved your login details.
How to Protect Yourself in 2026
The tools for stopping these attacks have gotten much better, but they only work if you actually use them. If you are traveling or working outside the office, these are your non-negotiables:
- Turn off “Auto-Connect”: Your phone and laptop are designed to be helpful by automatically joining open networks they’ve seen before. Turn this feature off. It prevents your device from blindly connecting to an “Evil Twin” network while your phone is sitting in your pocket.
- Use a Reputable VPN (Always): A Virtual Private Network (VPN) creates a secure, encrypted tunnel around your data. Even if a hacker intercepts your traffic, all they will see is an unreadable scramble of code.
- Hardware Security Keys: Passwords can be intercepted, but physical security keys (like a YubiKey) cannot. Even if a hacker steals your password in a MITM attack, they can’t log into your accounts because they don’t have the physical key plugged into your machine.
- Zero Trust Network Access (ZTNA): If you run a business, ditch the old-school corporate VPNs and look into ZTNA. It assumes every network (even your home office) is hostile and constantly verifies the user’s identity and device health before granting access to company apps.
- When in Doubt, Use Cellular: If you need to make a financial transaction or log into a sensitive work portal while at an airport or café, turn off the Wi-Fi. Use your phone’s 5G data or set it up as a personal hotspot. Cellular networks are incredibly difficult for standard hackers to intercept.
We can’t control the networks we connect to when we are out in the world, but we can absolutely control how our data travels across them. Treat every public Wi-Fi connection as if someone is listening—because there is a good chance they are.

